German Bundestag President Targeted in Signal Phishing Hack, Wider Campaign Hits European Politicians
Published on Reflecto News | World News | Cybersecurity & Intelligence
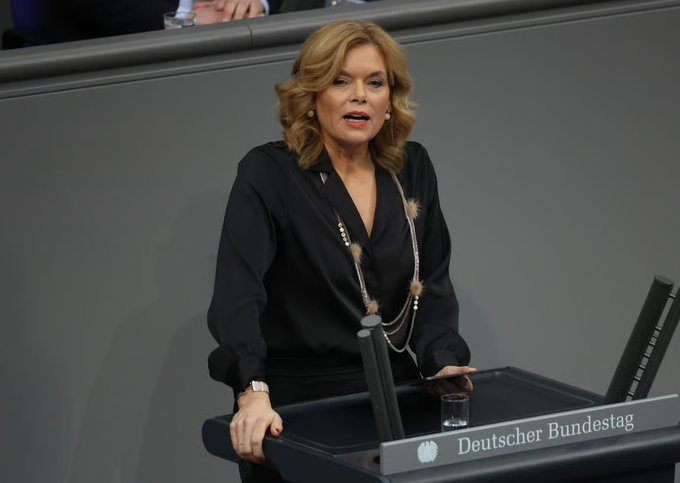
Germany’s Bundestag President Julia Klöckner was reportedly targeted in a sophisticated phishing attack on the messaging app Signal, part of a wider campaign aimed at European politicians, according to an investigation by Der Spiegel. The hackers posed as official Signal support personnel to trick users into revealing their PIN codes, potentially compromising their accounts .
Klöckner, a senior member of the Christian Democratic Union (CDU), was participating in a group chat that included party colleagues and, on some occasions, Chancellor Friedrich Merz. Investigators have found no evidence that the chancellor’s own device was compromised, but the breach of a senior parliamentary leader’s account has triggered alarm within German security services.
How the Hack Worked
The attack vector was social engineering, not a technical vulnerability in the Signal protocol itself. Hackers impersonated Signal support staff, contacting targeted individuals via text message and urging them to provide their PIN codes or other authentication information.
Once in control of an account, attackers could, in theory, monitor private communications, impersonate the user, or pivot to other contacts within the victim’s network. According to Der Spiegel, the campaign targeted multiple politicians across Europe, though the full scope of the operation remains under investigation.
Klöckner’s Role and Merz’s Proximity
As Bundestag President, Klöckner is the second-highest ranking official in Germany after Federal President Frank-Walter Steinmeier. Her role gives her access to sensitive political deliberations, including those within the CDU parliamentary group.
Klöckner was part of a CDU leadership chat group that included multiple high-ranking members. Chancellor Merz was also a participant in some group conversations, though forensic investigators have found no evidence that his device was compromised or that his communications were accessed.
A Wider European Campaign
The attack on Klöckner was not isolated. German security officials have been tracking a series of phishing attempts targeting political figures across the continent.
| Target | Platform | Status |
|---|---|---|
| Julia Klöckner (Germany) | Signal | Compromised |
| Multiple European politicians | Signal | Under investigation |
| Various (unspecified) | WhatsApp, Signal, Telegram | Suspected espionage |
The campaign bears hallmarks of state-sponsored intelligence activity, though investigators have not publicly attributed the attacks. Russia and other adversaries have previously been linked to cyber operations targeting Western political figures.
Signal’s Security Reputation
Signal is widely considered one of the most secure consumer messaging apps, with end-to-end encryption and a privacy-focused design. However, as these attacks demonstrate, even the most secure app cannot fully protect users against sophisticated social engineering.
German cybersecurity authorities have issued guidelines urging public officials to enable Signal’s “registration lock” feature, which requires a PIN to re-register an account on a new device. Officials are also being reminded to treat unsolicited “support” requests with extreme skepticism.
Official Response
The German Interior Ministry confirmed it was aware of the report and that security authorities were investigating the incident. A spokesperson for the Bundestag stated that Klöckner “immediately took appropriate security measures” upon discovering the compromise.
Chancellor Merz’s office declined to comment on the security status of his personal communications, citing security protocols.
What Comes Next
German intelligence is working to determine if the attackers successfully accessed Klöckner’s messages and, if so, what information they may have obtained. Investigators are also working to identify whether other German officials were similarly targeted.
The attack highlights the vulnerability of even security-conscious political figures to social engineering. As spy agencies increasingly target the personal communications of government officials, the line between secure technology and human fallibility remains the weakest link in the chain.
Frequently Asked Questions (FAQs)
1. Was Chancellor Merz’s phone compromised?
Investigators have found no evidence that Merz’s device was compromised or that his communications were accessed.
2. What kind of hack was it?
The attack was a phishing scheme, not a technical breach of Signal’s encryption. Hackers posed as Signal support staff to trick Klöckner into revealing her PIN code.
3. What is Signal’s registration lock?
The feature requires users to enter a PIN to re-register their account on a new device, making it more difficult for attackers to hijack accounts even if they have compromised credentials.
4. Who is behind the hack?
Investigators have not publicly attributed the attacks, but the campaign’s sophistication and targeting of European politicians have led to speculation of state-sponsored activity.
5. What should Signal users do to protect themselves?
Users should enable registration lock, use strong and unique PINs, and never respond to unsolicited requests for authentication information, even if they appear to come from official sources.
Stay informed with Reflecto News – Your trusted source for breaking cybersecurity and intelligence reporting. Subscribe for real-time updates on digital threats, state-sponsored hacking, and global security.